In today‘s installment of #BSidesMunich2025 – NEINth Edition, we focus on how initial access brokers say, „NO!“ to perimeter defenses and lower the barrier of entry for cyber criminals to gain access to companies networks.
## What is an initial access broker?
An initial access broker (IAB) is a business where participants focus on gaining initial access to a victim company’s systems and sell this access to other cyber criminals. They make money not by defrauding their victims, but by selling the access that they have won. This business model allows initial access brokers to focus on their core competency – gaining initial access; specializing, competing and innovating in this area.
## How do IABs gain initial access?
Initial access brokers use a variety of methods to gain initial access. They have been known to use low touch methods such as exploiting technical weaknesses in VPNs, RDP or websites to gain an initial foothold. They compromise user accounts using standard authentication attacks, credential dumps, XX-ishing (see: https://social.bsidesmunich.org/click-that-button-no/) and malware deployment.
## How do IABs operate the business?
The IAB business is relatively new, and has matured rapidly over the past few years. IABs offer their access via darknet marketplaces, they may have standing contracts with ransomware groups, they may contact interested parties directly. When selling access, IABs provide key information to their consumers about what type of access they are selling. They describe the technique used for access, user privilege level gained, industry, business size, region, etc. This helps their consumers make better decisions on who to target for biggest profit with the least chance of getting caught.
## Defending against IABs:
Naturally defenses against IABs include:
– keeping patches up-to-date in Internet-facing systems
– placing Internet-facing web applications behind an application firewall
– running endpoint protection on Internet-facing systems
– actively managing vulnerabilities on those systems
– implementing phishing resistant multi-factor authentication
– utilize threat intelligence to keep on top of latest indicators of compromise
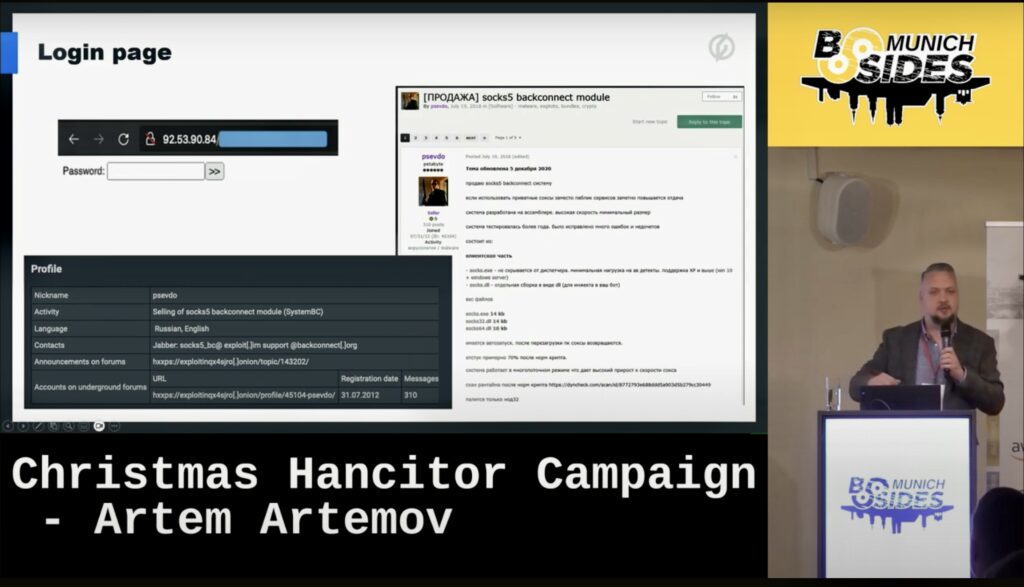
To give a concrete example of how (enhanced) threat intelligence can help reduce the full impact of attacks that come after initial access, see Artem Artemov‘s 2023 BSides Munich fascinating presentation, „Christmas Hancitor Campaign“. https://youtu.be/-N67xrL82L8?feature=shared
References:
https://www.cisecurity.org/insights/blog/initial-access-brokers-how-theyre-changing-cybercrime
https://cyberint.com/blog/other/initial-access-brokers-the-hard-facts/