In today’ installment of #BSidesMunich2025 NEINth Edition, we focus on the real-time „NO“ of protect, detect and respond:
– Endpoint Detection and Response (EDR) and
– Extended Detection and Response (XDR).
These are real-time, intelligent solutions built to detect and stop modern attacks before they cause damage.
What Is EDR?
EDR equips each device—like laptops or servers—with continuous monitoring, behavioral threat detection, and fast incident response. It’s designed to spot known and unknown threats, and quickly isolate affected machines.
Main benefits:
– Detects suspicious behavior beyond malware signatures
– Sends real-time alerts and can isolate infected devices automatically
– Allows detailed investigation into security incidents
What Is XDR (Extended Detection and Response)?
XDR takes a broader view by collecting and analyzing data from endpoints, cloud systems, email, identities, and networks. It connects events across systems to uncover coordinated attacks that isolated tools may miss.
Key advantages:
– Sees across systems, not just endpoints
– Links different threat signals for better context
– Speeds up response with automation and less noise
How EDR and XDR Compare to Traditional Security
Traditional tools—like antivirus, firewalls, and manual log review—mostly detect known threats and work in silos. In contrast:
– EDR spots both known and unknown threats using behavior analysis
– XDR looks across all systems to detect complex, multi-step attacks
– Both provide faster, more automated response than manual tools
– Can incorporate threat intelligence (see last week‘s article: https://social.bsidesmunich.org/proactively-saying-no/)
Why This Matters
Modern threats are more advanced, automated, and coordinated. You need a security approach that’s equally agile. EDR and XDR help IT teams detect threats sooner, respond faster, and minimize business disruption.
Are EDR and XDR 100% Effective?
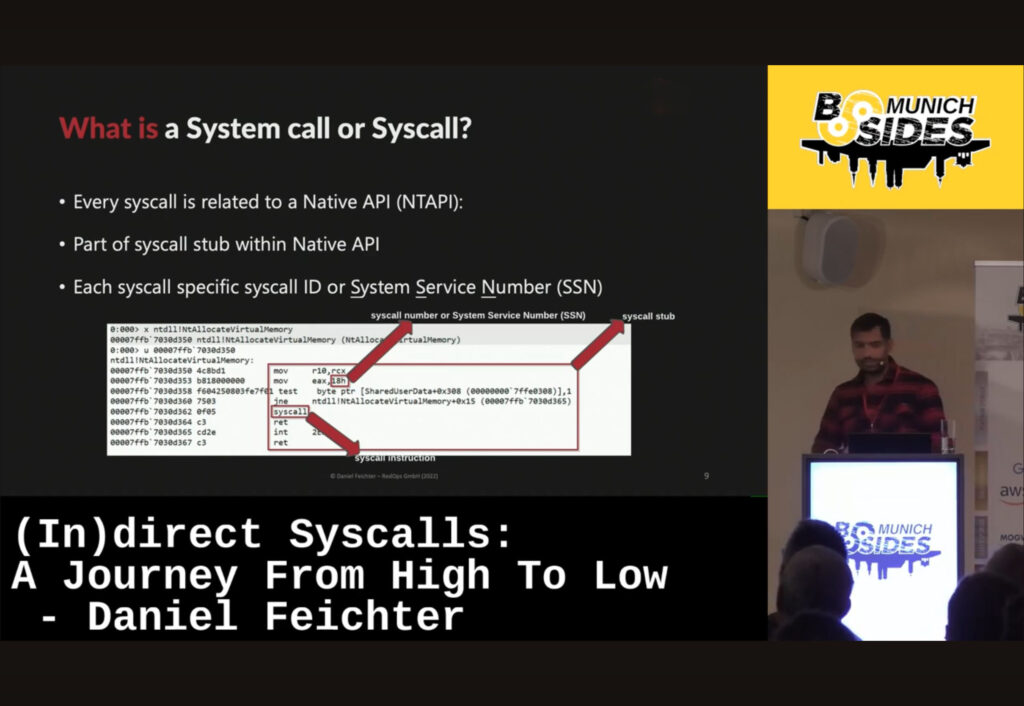
While EDR and XDR tools are continuously being improved, attackers still try to find weaknesses that will help bypass defenses. Luckily, there are skilled security researchers who help evaluate the tools‘ weaknesses so that they can be improved. This requires a low-level understanding of EDR/XDR functions and how interprocess communication works. See, for example, Daniel Feichter‘s presentation from 2023 BSides Munich, „(In)direct Syscalls: A journey from high to low“. https://www.youtube.com/watch?v=lyYzSKMPD4w
Inspired to submit a CFP idea? Learn more under: https://2025.bsidesmunich.org/callforpapers/